Introduction to the YubiKey Series
Where applicable, throughout this guide, the YubiKey 5 Series, the YubiKey 5 FIPS Series, the YubiKey 5 CCN Series, and the YubiKey 5 Enhanced PIN Series are referred to collectively as the YubiKey 5 Series, because all these YubiKeys share the same hardware base and many firmware features.
Also described in this guide are the YubiKey Bio Series and the Yubico Security Key Series.
This topic introduces:
- YubiKey 5 Series
- YubiKey 5 FIPS Series
- YubiKey 5 CCN Series
- YubiKey 5 Enhanced PIN Series
- YubiKey Bio Series
- Security Key Series
- Firmware Certifications
For a convenient way of comparing YubiKeys in 5 Series, Bio Series, and Security Keys Series, see Yubico’s YubiKey Comparison Chart.
YubiKey Series Form Factors
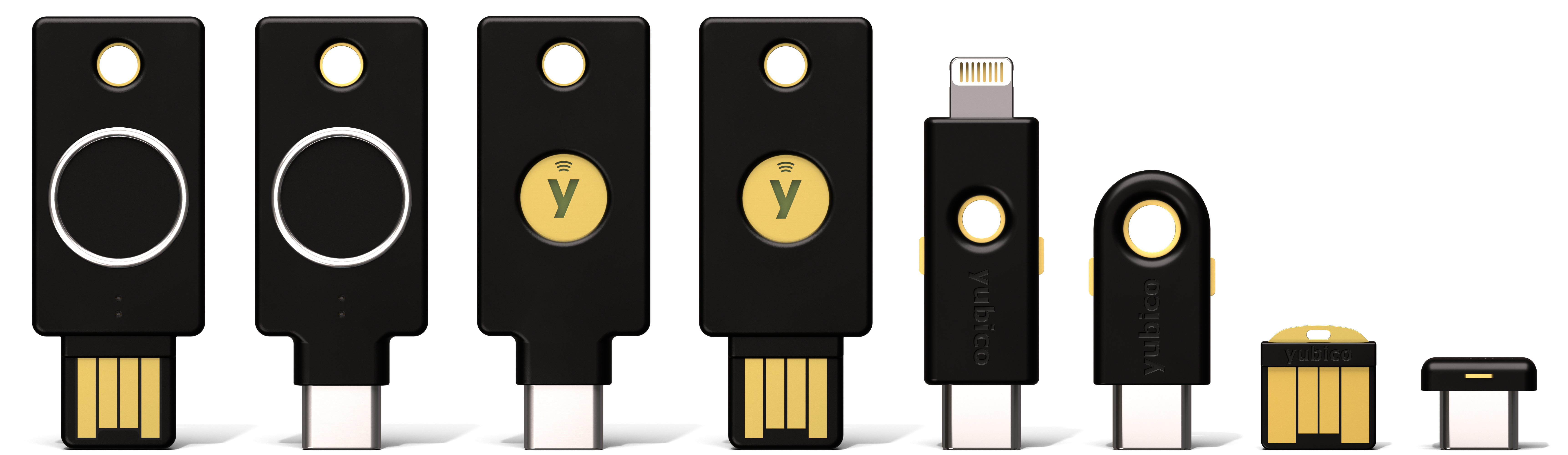
The following table lists for each YubiKey Series: supported form factors (in order matching the image) and minimum firmware version where the YubiKey series first became available on the listed form factor.
| YubiKey Series | 5 Bio | 5C Bio | 5C NFC | 5 NFC | 5Ci | 5C | 5 Nano | 5C Nano |
|---|---|---|---|---|---|---|---|---|
| Standard | 5.2.x | 5.0.x | 5.3.x | 5.0.x | 5.0.x | 5.0.x | ||
| FIPS | 5.4.2 | 5.4.2 | 5.4.2 | 5.4.2 | 5.4.2 | 5.4.2 | ||
| Enhanced PIN | 5.7.4 | 5.7.4 | ||||||
| CCN | 5.7.4 | 5.7.4 | ||||||
Bio FIDO
Edition
|
5.5.x 5.5.x | 5.5.x 5.5.x | ||||||
Bio Multi-
Protocol Ed.
|
5.5.x | 5.5.x | ||||||
| Security Key | 5.4.x | 5.0.x | ||||||
Security Key
Enterprise Ed.
|
5.4.x | 5.0.x |
Where form factor codes indicate an interface type. See YubiKey Connection Interfaces.
- NFC - Near Field Communication: 5 NFC, 5C NFC
- C - USB-C connector: 5C Bio, 5C NFC, 5Ci, 5C, 5C Nano
- Ci - Apple lightning connector: 5Ci
- Bio - Finger print sensor: 5 Bio, 5C Bio
- No extra code - USB-A connector: 5 Bio, 5 NFC, 5 Nano
For a quick start, to register your YubiKey with supported applications and services, see Set up your YubiKey
YubiKey 5 Series
The YubiKey 5 Series security keys offer strong authentication with support for multiple protocols, including FIDO2, which is the new standard that enables the replacement of password-based authentication. The YubiKey strengthens security by replacing passwords with strong hardware-based authentication using public key cryptography.
For those who just want to use a YubiKey without programming anything, the most useful part of this guide is Understanding the USB Interfaces. This topic describes how the YubiKey connects and indicates what it can connect to.
For an overview on setting up two-step verification in a typical case, see Google on using a security key for 2-step verification.
The full list of the services that work with YubiKeys is on Yubico’s Works With YubiKey page.
Most of the rest of this guide targets systems integrators, IT teams, or developers who expect to integrate support for YubiKeys into their environment.
Protocols and Applications lists the YubiKey 5 Series functionalities and capabilities by protocol:
Note
It is the firmware version that determines which of the more specialized functionalities and capabilities are available on your YubiKey. See Firmware Certifications.
Yubico Authenticator is one of the tools most commonly used to configure YubiKeys, so for a complete breakdown of Yubico Authenticator functionality by platform and connection type for each YubiKey model, see the Yubico Authenticator Functionality table.
The Yubico ykman CLI (command line interface) is another cross-platform tool for advanced management and configuration of all YubiKey applications (FIDO2, FIDO U2F, PIV, Yubico OTP, YubiHSM Auth, OpenPGP, OATH, Security Domain). See the YubiKey Manager (ykman) CLI Guide.
For a list of YubiKey 5 Series specifications, see the YubiKey 5 Series Product Brief.
YubiKey 5 FIPS Series
Federal Information Processing Standards (FIPS) are developed by the United States government for use in computer systems to establish requirements such as ensuring computer security and interoperability. The National Institute of Standards and Technology (NIST) and the Canadian Centre for Cyber Security (CCCS) run the NIST Cryptographic Module Validation Program (CMVP) as a collaborative effort.
FIPS certification demonstrates that a product has gone through a rigorous audit process and adheres to a security standard that can be measured and quantified.
Many government organizations and government contractors are required to use FIPS-approved products, as are highly-regulated industries in general. Other countries also recognize FIPS 140-3 and FIPS 140-2. For the U.S. government, the default is that FIPS is required.
Note
- Effective May 22 2026, YubiKey 5 FIPS Series with firmware 5.7.4 was NIST certified for FIPS 140-3.
- Effective May 2026, YubiKey 5 FIPS Series with firmware 5.4.x and NIST FIPS 140-2 certification moved to Sunset List.
- Effective September 22, 2026, All NIST FIPS 140-2 certification will be moved to the Historical List.
For a list of YubiKey 5 FIPS Series specifications, see the YubiKey 5 FIPS Series Product Brief.
See also in this guide, YubiKey 5 FIPS Series Features and NIST Certification: FIPS.
Do You Require FIPS Keys?
If you do not have a security auditor, and/or the auditor does not have a compliance requirement, you probably do not need FIPS. The standard line of YubiKeys (the non-FIPS series) offers the same security, algorithms, and functionality. The standard line also evolves at a much more rapid pace because it does not need to complete an exhaustive validation process, which commonly takes a year or more. Yubico can release standard firmware with new features and enhancements at any time, whereas FIPS-certified products must go through the FIPS validation process every time there is a firmware change.
YubiKey 5 CCN Series
The YubiKey 5 CCN Series is a standard YubiKey 5 Series key running firmware version 5.7.4 that is certified by the National Cryptologic Centre (CCN). This certification enables Spanish public organizations to comply with Royal Decree/Real Decreto 311/2022.
The YubiKey 5 CCN Series has been added to the CPSTIC catalog, Catálogo de Productos y Servicios de Seguridad de las Tecnologías de la Información y la Comunicación (CPSTIC), Yubikey 5 CCN Serieis 5.7.4, in compliance with Guía de Seguridad de las TIC, CCN-STIC 105.
To meet the CCN requirements, deploy the YubiKey CCN Series in accordance with the following:
- CCN compliance is focused on strong cryptographic authentication methods, specifically FIDO2 and PIV. Other protocols are not covered by CCN requirements.
- FIDO2 - Use PINs to protect all discoverable credentials.
- PIV - Use either RSA 3072 bytes and above or ECC based private keys.
- PIV - Change PIN, PUK, and Management keys from default. Block PUK codes if they are not required.
See also Yubico Support:
YubiKey 5 Enhanced PIN Series
The YubiKey 5 Enhanced PIN Series provides a standard YubiKey 5 Series key with fixed settings for 6 character minimum PIN length, PIN complexity, and always on verification.
Based on the YubiKey 5 Series, the Enhanced PIN Series features include:
Uses the FIDO (FIDO2/FIDO U2F) protocol. See FIDO2.
Is available in USB-A + NFC and USB-C + NFC form factors. See YubiKey 5 Enhanced PIN Series.
Ships with firmware version 5.7.4 or later. See Firmware Overview.
Has a serial number to enable asset tracking.
The serial number is on the back of the key and can also be read programmatically through the FIDO HID (Human Interface Device) interface.
Enables access to the serial number over CCID running firmware version 5.7.x. See CCID with USB.
The serial number is retrievable by client software in Windows without requiring elevated privileges (admin rights) since the YubiKey management application is accessible via CCID, which enables use cases where client software needs to read the serial number of the authenticator.
Enforces PIN Complexity. This cannot be changed.
Increases in the minimum FIDO pin length to 6. See Minimum PIN Length.
Enforces user verification always on, Always Require User Verification.
For a list of YubiKey 5 Enhanced PIN Series specifications, see the YubiKey 5 Series Product Brief.
For AAGUID, see YubiKey hardware FIDO2 AAGUIDs.
YubiKey Bio Series
The YubiKey Bio Series offers the familiar YubiKey experience users have come to know and trust, but adds the convenience of a new biometric touch feature. The following is a summary of the features; for complete explanations, see YubiKey Bio Series Specifics.
New York State’s Department of Financial Services (DFS) advises that instead of using a traditional fingerprint or other biometric authentication system, the services regulated by DFS should consider using an authentication factor that employs technology with liveness detection or texture analysis to verify that a print or other biometric factor comes from a live person. This is what the new biometric touch feature provides.
The series is comprised of four keys:
- The YubiKey Bio - FIDO Edition (USB-A form factor)
- The YubiKey C Bio - FIDO Edition (USB-C form factor)
- The YubiKey Bio - Multi-protocol Edition (USB-A form factor)
- The YubiKey C Bio - Multi-protocol Edition (USB-C form factor)
Up to five fingerprints can be stored on a YubiKey Bio.
For a list of YubiKey Bio Series specifications, see the YubiKey Bio Series Product Brief.
For AAGUIDs, see YubiKey hardware FIDO2 AAGUIDs.
YubiKey Bio Multi-protocol Edition
The YubiKey Bio Multi-protocol Edition is a new product that combines the ease of use of the YubiKey Bio FIDO Edition with a PIV-like smart card interface and unified PIN and fingerprint templates. This unique combination produces a portable authenticator with the convenience of biometric authentication and support for desktop login.
The YubiKey Bio Multi-protocol Edition takes a novel approach to PINs and fingerprints by using the same PIN and fingerprint templates for both FIDO and smart card. The resulting experience is seamless provisioning and use across both desktop sign-in and web use cases. This thereby eliminates the need for the user to enroll fingerprints multiple times or manage individual PINs.
Security Key Series
The Security Key Series are only available with the FIDO (FIDO2/FIDO U2F) protocol and is only available in USB-A + NFC and USB-C + NFC form factors. The lastest FIDO updates are included with the latest YubiKey firmware on all Sercurity Key Series.
The Security Key Series - Enterprise Edition includes the features of the Security Key Series and has the following additional updates:
A serial number to enable asset tracking. The serial number is on the back of the key and can also be read programmatically through the FIDO HID interface.
Access the serial number over CCID for Security Key - Enterprise Edition running firmware version 5.7.x. See CCID with USB.
The serial number is retrievable by client software in Windows without requiring elevated privileges (admin rights) since the YubiKey management application is accessible via CCID, which enables use cases where client software needs to read the serial number of the authenticator. This change was introduced in 5.7.0.
PIN Complexity turned on by default (and cannot be turned off).
Increase in minimum FIDO pin length to 6. See Minimum PIN Length.
Capability
|
5.7.x
Enterprise Edition
|
5.7.x
|
5.4.x
Enterprise Edition
|
5.0.x-5.4.x
|
|---|---|---|---|---|
| Serial Number | Yes | No | Yes | No |
| Serial Number over CCID | Yes | No | No | No |
| PIN Complexity | Yes | No | No | No |
| FIDO Minimum PIN Length | 6 | 4 | 4 | 4 |
For a list of Yubico Security Key Series specifications, see the Security Key Series Product Brief.
For AAGUIDs, see YubiKey hardware FIDO2 AAGUIDs.
YubiKey 5 CSPN Series
Important
The YubiKey 5 CSPN Series has been discontinued.
Instructions on how to configure and use the YubiKey 5 in compliance with CSPN (“Certificat de Sécurité de Premier Niveau” [RD1]) are given in YubiKey 5 CSPN Series Specifics.
For each YubiKey application that requires specific configuration, there is a short introduction, the required settings to achieve the target, and a technical description of the configuration.
Firmware Certifications
For a summary overview of the firmware features, see Firmware Overview, which includes the capability matrices, listing the features and form factors available per firmware version for each of the products in the YubiKey 5 Series and the Security Key Series.
For more in-depth information about:
- 5.7.4 Firmware - FIPS Series, most recent firmware release
- 5.7 and 5.6 Firmware Prior to 5.7.4
- Pre-5.6 Firmware Specifics
The firmware version on a YubiKey or a Security Key determines whether or not a feature or a capability is available to that device. The quickest and most convenient way to determine your device’s firmware version is to use either the Yubico Authenticator with its intuitive and easy-to-use (GUI) interface or ykman the lightweight command line (CLI) software package installable on many OSs.
Note
Yubico periodically updates its firmware to take advantage of features and capabilities introduced into the ecosystem. YubiKeys are programmed in Yubico’s facilities with the latest available firmware. Once programmed, YubiKeys cannot be updated to another version. The firmware cannot be altered or removed from a YubiKey.
FIDO Authenticator Supported Certifications
The certifications that are supported by a FIDO authenticator can be returned in the certifications member of an authenticatorGetInfo response as set out in paragraph 7.3.1. Authenticator Actions of the Client to Authenticator Protocol (CTAP) Review Draft of March 09, 2021.
NIST Certification: FIPS
Yubico submitted the firmware for releases 5.7.4 to NIST and the organization approved the certification for FIPS 140-3 Security Levels 2. The certificate can be found at Cryptographic Module Validation Program (CMVP) Certificate #5291.
Yubico submitted the firmware for releases 5.4.2 and 5.4.3 to NIST and the organization approved the certification. The certificates can be found here.
For more information about the YubiKey 5 FIPS Series, see YubiKey 5 FIPS Series Features.
CCN Certification: 5 Series NFC
Yubico submitted the firmware for release 5.7.4 to the Certification Organization for the National Cryptologic Centre (CCN) and the organization approved the certification. The CCN Certification is published in the CPSTIC catalog, Catálogo de Productos y Servicios de Seguridad de las Tecnologías de la Información y la Comunicación (CPSTIC), Yubikey 5 CCN Serieis 5.7.4.
For more information about the YubiKey 5 CCN Series, see YubiKey 5 CCN Series.
ANSI Certification: CSPN
The YubiKey 5 CSPN Series has been discontinued.
Yubico submitted release 5.4.2 to ANSSI for certification and the organization approved the certification. For more information about the YubiKey 5 CSPN Series, see YubiKey 5 CSPN Series.