Getting Started
The purpose of this tutorial is to demonstrate basic functionalities of different key types: Authentication Key, Asymmetric Key and Wrap Key. We start with a fresh YubiHSM 2 configuration and we proceed in generating a new Authentication Key. Then we generate an Asymmetric Key for signing purposes. We sign an arbitrary amount of data and verify that our signature is correct. Part of this documentation is to demonstrate how to backup a key on a second YubiHSM 2. We do so by wrapping the Asymmetric Key and re-importing it into the same device.
This tutorial covers:
Initial Provisioning and Deployment for HMAC, PKCS11, or RSA
Backup and Restore with YubiHSM Backup Keys
- Backing up and Restoring YubiHSM 2 Keys
- Backing up and Restoring Key Material
Before proceeding with this document you should be familiar with concepts such as: Sessions, Domains, Capabilities described in Core Concepts.
Note
The following code samples have arbitrary line-breaks to prevent them from running off the page.
Set Up the YubiHSM 2 Environment
- Get the latest binaries from SDK download YubiHSM2/Releases.
- Install all libraries.
- Make sure your device is accessible by the connector. This is accomplished either by running the connector as a superuser or by using an appropriate udev_rule.
Install the YubiHSM 2 Tools and Software
To complete the procedures in this guide, install the YubiHSM 2 tools and software that will be needed for this.
Tip
A generic prompt, $, is used in command line examples in this document. Depending on your command line application, your prompt may be different.
The following YubiHSM items of software are used in this guide. They are included as part of the archive file you downloaded.
Unzip the downloaded archives of the SDK containing the YubiHSM libraries and tools and move the contents to an appropriate location.
Complete the step for your operating system.
On your Windows system, run both installers:
yubihsm-cngprovider-windows-amd64.msi(YubiHSM Key Storage Provider)yubihsm-connector-windows-amd64.msi(YubiHSM Connector for Windows)
On a Debian-based system, run the following command:
$ dpkg -i ./libykhsmauth1_*.deb ./libyubihsm-usb1_*.deb ./libyubihsm-http1_*.deb ./libyubihsm1_*.deb ./yubihsm-shell_*.debOn a Redhat-based system, run the following command:
$ yum install ./yubihsm-shell-*.rpm
(Windows system) Set the ADCS service dependency for the YubiHSM Connector service via an elevated/admin Windows Command Prompt. This prevents an error which occurs if the ADCS services start before the YubiHSM connector is running.
- List the current dependencies with
sc qc “certsvc”
> sc qc “certsvc” [SC] QueryServiceConfig SUCCESS SERVICE_NAME: certsvc TYPE : 110 WIN32_OWN_PROCESS (interactive) START_TYPE : 2 AUTO_START ERROR_CONTROL : 1 NORMAL BINARY_PATH_NAME : C:\Windows\system32\certsrv.exe LOAD_ORDER_GROUP : TAG : 0 DISPLAY_NAME : Active Directory Certificate Services DEPENDENCIES : SERVICE_START_NAME : localSystem
Add the YubiHSM Connector dependency to ADCS with the command:
sc config "certsvc" depend="yhconsrv"> sc config "certsvc" depend="yhconsrv" [SC] ChangeServiceConfig SUCCESS
After the command is entered, the dependency can be verified with
sc qc “certsvc”[SC] QueryServiceConfig SUCCESS SERVICE_NAME: certsvc TYPE : 110 WIN32_OWN_PROCESS (interactive) START_TYPE : 2 AUTO_START ERROR_CONTROL : 1 NORMAL BINARY_PATH_NAME : C:\Windows\system32\certsrv.exe LOAD_ORDER_GROUP : TAG : 0 DISPLAY_NAME : Active Directory Certificate Services DEPENDENCIES : yhconsrv SERVICE_START_NAME : localSystem
To remove dependencies for ACDS, use the same command for adding dependencies with a blank depend field:
sc config "certsvc" depend=""
- List the current dependencies with
Verify the Default Configuration of the YubiHSM 2
Verify the results of the YubiHSM Setup program using the YubiHSM Shell program. Log in using the application authentication key.
The YubiHSM 2 device comes with a single factory-installed authentication key whose default password is password. As part of the configuration in this guide, this default authentication key will be destroyed. If the YubiHSM 2 is reset to its default configuration, any non factory-installed objects stored on it are also destroyed. Reset instructions can be found in Reset YubiHSM to Factory Settings.
We reiterate that you will need two YubiHSM 2 devices to complete all steps of this guide, because you will be deploying the first device and creating a backup of all key material on the second device.
These steps also verify that neither of the YubiHSM 2 devices have been tampered with.
To verify that YubiHSM 2 devices still have the default configuration by following the steps below:
Verify the YubiHSM 2 setup, in your Command Prompt, run the following command:
$ yubihsm-shellDo one of the following:
- If the application that calls the YubiHSM Connector is running on a local host, start the Connector with the command
yubihsm-connectorwithout additional parameters. In Windows Server 2012 SP2 or higher,yubihsm-connector.exeis located inC:\Program Files\YubiHSM Connector\. - If the application is running on a VM or a different server, start the YubiHSM Connector on the host operating system in networking mode. For example, if the host machine’s IP address is
192.168.100.252, launch the Connector on the host OS with the commandyubihsm-connector -l 192.168.100.252:12345
Tip
For testing or debugging the YubiHSM Connector, the flag
-dcan be set.- If the application that calls the YubiHSM Connector is running on a local host, start the Connector with the command
To gain shell access to the YubiHSM 2, launch the YubiHSM Shell program:
Open a Command Prompt.
Run the command
yubihsm-shell.If a networked Connector is used, set the parameter
--connect <connector URL>.If the YubiHSM Connector is running on a host machine to which the YubiHSM 2 is physically connected, start the YubiHSM Shell program in networked mode.
$ yubihsm-shell --connector http://192.168.100.252:12345
where –
The host server’s IP address is 192.168.100.252
Tip
For testing or debugging the YubiHSM Shell, the flag
-dcan be set.To connect to the YubiHSM 2, at the
yubihsmcommand line, typeconnect. A message saying that you have a successful connection is displayed.To open a session with the YubiHSM 2, type
session open 1(where1is the ID of the default authentication key pre-installed on the device).Type in the default password:
password. A message confirming that the session has been set up successfully is displayed.You now have an administrative connection to the YubiHSM 2 and you can list the objects available by typing
list objects 0and pressing Enter. Your results should be similar to the following:Found 3 object(s) id: 0x0002, type: wrap-key, sequence: 0 id: 0x0003, type: authentication-key, sequence: 0 id: 0x0004, type: authentication-key, sequence: 0
As you can see by looking at their IDs, these objects correspond to the wrap key, the application authentication key and the audit key that were just created.
To obtain more information about any of the objects and its capabilities — for example, the application authentication key (object ID 3) — run the
objectinfocommand with the appropriate ID format, for example:yubihsm> get objectinfo 0 3 authentication-key
The response you receive should look similar to the following:
id: 0x0003, type: authentication-key, algorithm: aes128-yubico-authentication, label: "Application auth key", length: 40, domains: 1, sequence: 0, origin: imported, capabilities: exportable-under-wrap:generate-asymmetric-key: sign-attestation-certificate:sign-pkcs:sign-pss:sign-ecdsa, delegated_capabilities:exportable-under-wrap: generate-asymmetric-key:sign-attestation-certificate:sign-pkcs: sign-pss:sign-ecdsa
Review the responses to confirm that YubiHSM 2 has now been configured to:
- Generate asymmetric objects
- Compute signatures using RSA-PKCS1v1.5
- Compute signatures using RSA-PSS
- Export other objects under wrap
- Import wrapped objects
- Mark an object as exportable under wrap
In addition, this object (the application authentication key, object ID 3) also has delegated capabilities that can be bestowed on other objects that it creates. For more information on delegated capabilities, see Capabilities.
To exit, type
quit.
Physical YubiHSM Care
This section describes general information about packaging, identifying, and caring for your YubiHSM.
Verify the YubiHSM and Packaging
The YubiHSM has its own packaging style. Be sure you received the YubiHSM you ordered.
When you receive your YubiHSM, check that the packaging has not been tampered with.
Check that the YubiHSM arrives in the correct Yubico packaging.
See YubiKey packaging for images and description of the packaging used for YubiHSM 2 and YubiHSM 2 FIPS.
Check all the packaging components:
- The security seal on the back of the sleeve is not torn.
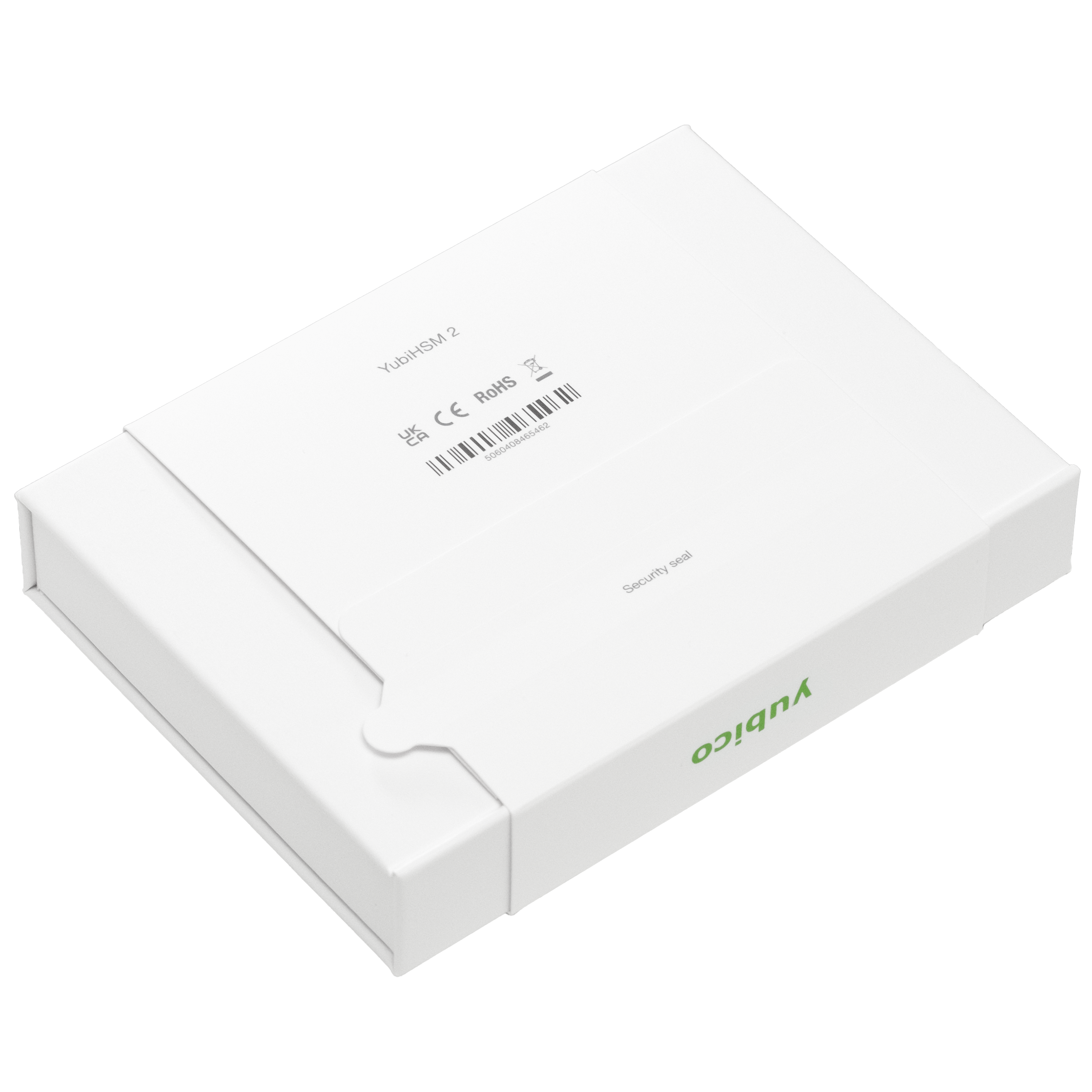
YubiHSM packaging with intact security seal
- The outer box cardboard box is not broken.
- The inner card tray show no signs of wear or tear

YubiHSM packaging with intact inner card tray
If you suspect any tampering, Submit a request.
When in doubt, you can also easily test that your YubiHSM is a genuine YubiHSM.
Go to Verify your Yubikey.
Insert your YubiHSM.
Click Verify Device.
The response shows images your YubiHSM form factor and firmware version.
YubiHSM ID Numbers
Various security protocols and use cases require valid devices identification. To locate the ID numbers:
For USB Product Identifier (PID), see How to find the USB Product ID (PID) of your YubiKey and YubiKey USB ID values.
Care and Cleaning
YubiHSMs are IP68-rated. This means you can expect the YubiHSM to not allow ingress of dust up to level 6 and water resistance up to level 8 as defined by the International Electrotechnical Commission, for ingress protection (IP). See European Standards, BS EN 60529:1992+A2:2013.
To clean the YubiHSM, use wipes impregnated with no more than 70% isopropyl alcohol.
Connect to the YubiHSM 2
Start the Connector
To physically reset the YubiHSM 2 insert the device while holding the touch sensor for 10 seconds. The following steps use the yubihsm-connector. Connection can also be made using the direct USB mode which is explained later in this document.
- Start the connector.
$ yubihsm-connector -dwhere –
-druns the connector in debug mode which may slow down the connector. It is not required for normal mode of operations.
- Check the status of your connector and device by using a browser to visit http://127.0.0.1:12345/connector/status.
Set Up YubiHSM 2 Connection
Connecting to the YubiHSM 2 device that is typically installed physically inside a system. The YubiHSM key is a USB-A device.
To connect to the YubiHSM 2 and perform tasks:
Preparation steps:
- Use one of the following to establish a physical connection.
- Network USB server.
- Virtual machines.
- USB over IP appliances.
- Compile the connector. See the README doc for the YubiHSM Connector.
Connection steps:
Start yubihsm-shell.
$ yubihsm-shellConnect to YubiHSM 2.
$ yubihsm> connect
Connect through Sessions with Applications
Many commands require a Session ID to be specified. To obtain a Session ID use the session open command followed by an Authentication Key ID and a derivation password.
By default the YubiHSM 2 comes with a pre-installed Authentication Key with Object ID 1 and derivation password password.
A Session is not a property of a specific Object, but rather it is used to describe a logical connection between an application and a device. Sessions are end-to-end encrypted and authenticated using Session Keys. These keys are derived from long-lived, pre-shared Authentication Key Objects as part of the sessions authentication process. The Session creation and authentication protocol is based on Global Platform SCP03.
On a single YubiHSM 2 it is possible to establish up to 16 independent and concurrent Sessions. Note that while multiple concurrent Sessions can be active at a given time, the device still serves as a rendezvous point. This means that time-consuming operations such as generating a long RSA key will block commands in other Sessions. Sessions are addressed with a number in the range [0-15].
Sessions have an expiration period of 30 seconds of inactivity in order to prevent resource starvation. After 30 seconds, the device will consider a Session inactive and will move it to the pool of re-usable Sessions. Whenever a command is executed on a given Session, the inactivity timer is reset, meaning that if a Session is being constantly used, it will not expire.
Some of the operations that can be performed on a YubiHSM 2 do not require a Session. The implication is that the command and its response will travel unencrypted to and from the device. These commands are only generic status commands, making Sessions required for any meaningful operation.
The long-lived keys required to derive Sessions can be explicitly used in the relevant commands. However, there are built-in functionalities to derive those keys from a password using 10,000 iterations of PBKDF2 with the salt Yubico, making the process more human-friendly. Every new or factory-reset YubiHSM 2 has a default Authentication Key with ID 1 and all Capabilities and all Domains set. This is equivalent to a superuser or an administrator. The long-lived keys for this Object are derived using the process previously described with the password password.
Warning
It is crucial to delete this well-known Authentication Key before deployment.
Open Session
To open a Session with this Authentication Key use:
yubihsm> session open 1 password
Created session 0
The Session ID is the number found in the line directly below a session open command.
where –
0 Is the Session ID. This value is used to address the newly created Session.
1 is the object ID of the pre-installed Authentication Key.
password is the password of the pre-installed Authentication Key.
Close Session
To close a Session use the command session close followed by the Session ID:
yubihsm> session close 0
where –
0 Is the Session ID.
List Session
To list the objects in the device use:
yubihsm> list objects 0
where–
0 Is the Session ID.
Note
If you have closed Session 0, the above command will not work. In that situation, open a new Session and use the new Session ID in the command above.
Initial Provisioning and Deployment for HMAC, PKCS11, or RSA
This topic covers operations pertaining to the initial provisioning and deployment of YubiHSM 2 devices.
Familiarity with the device, its features and capabilities is assumed.
Important
The YubiHSM 2 ships with a default Authentication Key with a well-known password. It is imperative that it is removed (single use case) or changed prior to production deployment.
See also:
- Add a New Authentication Key
- Generate an Asymmetric Key Object for Signing
- Export an Asymmetric Key Under Wrap
Known Usage Cases
When only a single application needs to be provisioned, Yubico recommends that all Authentication Keys and material be provisioned only with Capabilities specific to that use case.
Note
This type of deployment requires devices to be physically reset and re-provisioned (single use case) or changed should a new use case arise.
HMAC
Establish a session with the default Authentication Key.
yubihsm> connect Session keepalive set up to run every 15 seconds yubihsm> session open 1 password Created session 0
Create an Authentication Key for Auditing.
yubihsm> put authkey 0 0 "Audit auth key" all get-log-entries none $AUDIT_PASS Stored Authentication key 0xd054
Create a Wrap Key for importing application Authentication Keys and secrets.
yubihsm> get random 0 16 5b61e89468cc8f2a274715c78c3d4753 yubihsm> put wrapkey 0 0 "HMAC wrap Key" all import-wrapped sign-hmac:verify-hmac 5b61e89468cc8f2a274715c78c3d4753 Stored Wrap key 0xf09a
Create an Authentication Key for use with the above Wrap Key.
yubihsm> put authkey 0 0 "Provisioning HMAC wrap auth key" all import-wrapped none $WRAP_PASS Stored Authentication key 0xf10f
Delete the default Authentication Key.
yubihsm> delete 0 1 authentication-key
Create a wrapped Authentication Key and HMAC Key for the application.
echo -ne '\x5b\x61\xe8\x94\x68\xcc\x8f\x2a\x27\x47\x15\xc7\x8c\x3d\x47\x53' > wrap.key echo $HMAC_PASS | yubihsm-wrap -a aes128-yubico-authentication -c sign-hmac,verify-hmac -d 1 -l "HMAC auth key" -k wrap.key --in --out auth.out -e none echo -ne '\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b\x0b' > hmac.key yubihsm-wrap -a hmac-sha256 -c sign-hmac,verify-hmac -d 1 -l "HMAC key" -k wrap.key --in hmac.key --out hmac.out
Open a Session with the wrap Authentication Key.
yubihsm> session open 0xf10f $WRAP_PASS Created session 1
Import the two wrapped keys in the new Session.
yubihsm> put wrapped 1 0xf09a auth.out Object imported as 0x2a74 of type authentication-key yubihsm> put wrapped 1 0xf09a hmac.out Object imported as 0xd1a2 of type hmac-key
Open a session with the new application Authentication Key.
yubihsm> session open 0x2a74 $HMAC_PASS Created session 2
Run HMAC-SHA256 Test vector #1 and get expected output.
yubihsm> hmac 2 0xd1a2b0344c61d8db38535ca8afceaf0bf12b881dc200c9833da726e9376c2e32cff7 echo -ne '\x48\x69\x20\x54\x68\x65\x72\x65' | openssl dgst -hex -mac hmac -macopt hexkey:0b0b0b0b0b0b0b0b0b0b0b0b0b0b0b0b0b0b0b0b -sha256 (stdin)= b0344c61d8db38535ca8afceaf0bf12b881dc200c9833da726e9376c2e32cff7
PKCS11 / RSA
This example assumes that only RSA operations will be performed and that RSA keys will be generated on device over PKCS#11. For using the PKCS#11 a yubihsm\_pkcs11.conf file needs to exist and point at the desired connector.
Establish a Session with the default Authentication Key.
yubihsm> connect Session keepalive set up to run every 15 seconds yubihsm> session open 1 password Created session 0
Create an Authentication Key for Auditing.
yubihsm> put authkey 0 0 "Audit auth key" all audit none $AUDIT_PASS Stored Authentication key 0xd054
Optionally enable forced audits.
yubihsm> put option 0 force-audit 01
Create an Authentication Key for usage with the PKCS11 module.
yubihsm> put authkey 0 0 "PKCS11 RSA" 1 delete-asymmetric-key: generate-asymmetric-key:sign-pkcs:sign-pss sign-pkcs:sign-pss $PKCS11_PASS Stored Authentication key 0xf10f
Delete the default Authentication Key.
yubihsm> delete 0 1 authentication-key
Use pkcs11-tool to generate an RSA key.
pkcs11-tool --module /path/to/yubihsm_pkcs11.so -l --pin f10f${PKCS11_PASS} -k --key-type rsa:2048 --usage-sign --label "RSA key" Using slot 0 with a present token (0x0) Key pair generated: Private Key Object; RSA label: RSA key ID: e77d Usage: sign Public Key Object; RSA 2048 bits label: RSA key ID: e77d Usage: none
Add a New Authentication Key
Before moving on, make sure you are familiar with concepts of Capabilities and Domains
- For our example we are going to generate an Authentication Key with selected Capabilities and Domains. Learn more about existing key Types at Objects.
yubihsm> put authkey 0 2 yubico 1,2,3 generate-asymmetric-key,export-wrapped,get-pseudo-random,put-wrap-key,import-wrapped,delete-asymmetric-key,sign-ecdsa sign-ecdsa,exportable-under-wrap,export-wrapped,import-wrapped passwordwhere –
put authkeyis the command to create a new authentication key.
0is the session ID.
2is the ObjectID of the new authentication key.
yubicois the label of the new authentication key.
1,2,3is the domain where the new authentication key will operate within.
generate-asymmetric-key, export-wrapped,get-pseudo-random,put-wrap-key,import-wrapped,delete-asymmetric-key,sign-ecdsaare the capabilities for the new authentication key.
sign-ecdsa,exportable-under-wrap,export-wrapped,import-wrappedthe delegated capabilities for the new authentication key.
passwordis the password used to derive the new authentication key. This is the password you specify when opening a session with the YubiHSM using this authentication key.Important
export-wrappedallows the creation of Objects that can perform the EXPORT WRAPPED Command command.
exportable-under-wrapallows the creation of Objects that can be exported under wrap.Note
The command above has two distinct sets of Capabilities, separated by a space. This is because Authentication Keys, in addition to having regular Capabilities, also have Capabilities.
List all Objects to see the newly created Authentication Key.
yubihsm> list objects 0
where –
0the Session ID used for the open session.Next, let’s start using our newly created Authentication Key to establish an encrypted Session.
yubihsm> session open 2 password Created session 1where –
1is the Session ID assigned to the new Session. We will use this Session ID for most of the commands below. If at any time the Session is closed or expires because of inactivity, open a new one and use the correct Session ID.
2is the ObjectID of the authentication key used to open the session.
passwordis the password of the authentication key used to open the session.
Generate an Asymmetric Key Object for Signing
We now proceed to generate a new Asymmetric Key. In our example we will use this key to sign some data. We will also export the key under wrap to another YubiHSM, for backup purposes.
Specifically, we will ask the device to generate an Asymmetric Key with ID 100 and a given set of Domains and Capabilities. We will also specify the kind of Asymmetric Key that we would like to generate, an EC key using the NIST P-256 curve in this case.
The command is:
yubihsm> generate asymmetric 1 100 label_ecdsa_sign 1,2,3 exportable-under-wrap,sign-ecdsa ecp256
where –
generate is YubiHSM shell command.
asymmetric is the key type to be generated.
1 is the session ID.
100 is the key ID.
label_ecdsa_sign is the label for the new key object.
1,2,3 are the domains where the new key will be accessible.
exportable-under-wrap allows this key to be exported under wrap.
sign-ecdsa is allows this key to be used to perform ECDSA signature.
ecp256 specifies NIST P-256 curve for the key.
On success, we will see the message:
Generated Asymmetric key 0x0064
This signifies that an Asymmetric Key with ID 0x0064 (hexadecimal for 100) was generated.
Prepare to Sign With the New Asymmetric Key
- Assuming we have a file called
data.txtcontaining the data we would like to sign, we will sign it using ECDSA with the Asymmetric Key we generated in the previous step.
yubihsm> sign ecdsa 1 100 ecdsa-sha256 data.txtwhere –
1is the Session ID.
100is the key ID.By default the output is printed to the standard output and consists of a Base64-encoded signature like the one below.
MEUCIQDrBqS04LN5YdyWGiD4iaEjfl1dn+W4cl97uMMXDpoaiQIgEBe/G/FgP4cumnO3K2XWToAnPvnuVDOnqHPiuUS0q5g=
- This behavior can be changed by using the
set outformatandset informatcommands, and by specifying an additional output parameter to thesigncommand.
For now we will store the signature as it is in a temporary file so that we will be able to verify it later.
$ echo MEUCIQDrBqS04LN5YdyWGiD4iaEjfl1dn+W4cl97uMMXDpoaiQIgEBe/G/FgP4cumnO3K2XWToAnPvnuVDOnqHPiuUS0q5g= >signature.b64
- Next, we will extract the public key from the Asymmetric Key on the device and write it to the file
asymmetric_key.pub, so that we can use it to verify the signature we just created.
yubihsm> get pubkey 1 100 asymmetric_key.pub
- We are going to use OpenSSL for the verification process. Since the signature that we created before is in Base64 format, we need to convert it first. Do so with:
$ base64 -d signature.b64 >signature.bin
- It is now possible to verify the signature with OpenSSL.
$ openssl dgst -sha256 -signature signature.bin -verify asymmetric_key.pub data.txt Verified OK
Export an Asymmetric Key Under Wrap
Time to export the Asymmetric Key under wrap to a second YubiHSM 2 (in this example, we will export to the same YubiHSM for convenience).
To do that we need a Wrap Key, which fundamentally is an AES key. We use the random number generator built into the YubiHSM to generate the 16 bytes needed for an AES-128 key.
yubihsm> get random 1 16 9207653411df91fd36c12faa6886d5c4
Important
The result of this command (the bytes) is considered extremely sensitive data and should be stored safely, and preferably, separate from any production environment.
We can now store the Wrap Key on the device with ID 200 by doing:
yubihsm> put wrapkey 1 200 label_wrapkey 1,2,3 import-wrapped,export-wrapped sign-ecdsa, exportable-under-wrap 9207653411df91fd36c12faa6886d5c4
Note
For the upcoming
exportcommand to be successful, the Delegated Capabilities of the Wrap Key have to include the Capabilities of the Object being exported. Similarly, for theimportcommand to succeed the Delegated Capabilities of the Wrap Key have to include the Capabilities of the Object being imported.We can now export the Asymmetric Key with ID
100using the Wrap Key with ID200and save it to a file calledwrapped_asymmetric.key.yubihsm> get wrapped 1 200 asymmetric-key 100 wrapped_asymmetric.key
We are going to re-import the Asymmetric Key on the same device so we need to first delete the existing one.
yubihsm> delete 1 100 asymmetric-key
To import the wrapped EC key back into the YubiHSM use:
yubihsm> put wrapped 1 200 wrapped_asymmetric.key