Shipping Pre-enrolled Keys
This section describes how to work with shipments of pre-enrolled YubiKeys generated using the Yubico service FIDO Pre-reg available through identity provider (IdP or IDP) integration.
About FIDO Pre-reg
The FIDO Pre-reg service reduces the IT administrative burden and improves end-user experience by standardizing and streamlining YubiKey onboarding and account recovery, helping organizations become phishing-resistant.
With FIDO Pre-reg, the IT administrator (IT admin) for an organization can use the YubiEnterprise API together with an identity provider’s WebAuthn API and automated workflows to order pre-enrolled YubiKeys for end users. The YubiKeys are pre-enrolled and shipped directly to the specific end user who receives a randomly generated PIN separately, and can immediately authenticate using their YubiKey.
FIDO Pre-reg Integrations
Yubcio provides FIDO Pre-reg integrations for the following IdPs:
- Okta - see the FIDO Pre-reg with Okta Integration Guide.
- Microsoft Entra ID (Early Access) - see the FIDO Pre-reg with Microsoft Integration Guide.
- PingOne PingID and PingOne AIC - see the FIDO Pre-reg with PingOne Integration Guide.
Note
Currently you can only request one (1) YubiKey per shipment request using FIDO Pre-reg.
Managing Pre-enrolled Shipments
The following provides an overview of how to manage shipment requests for pre-enrolled YubiKeys.
Viewing Pre-enrolled Shipments
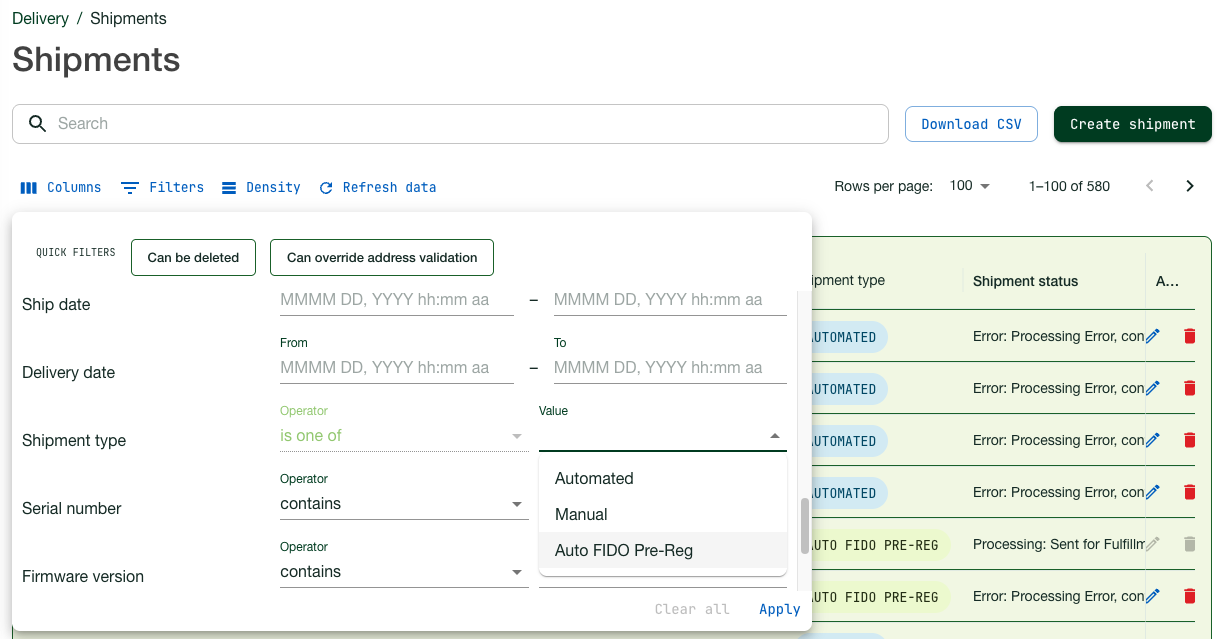
Just as for other types of shipment requests, you can monitor the status of pre-enrolled shipments for your organization in the Shipments page of the Customer Portal. Pre-enrolled shipments are indicated as AUTO FIDO PRE-REG in the Shipment type column on the page.
To locate a specific shipment of pre-enrolled YubiKeys, do the following:
- Use the Filters function to filter out pre-enrolled shipments. Click Filters, select “Auto FIDO Pre-reg” as Shipment type, and click Apply.
- You can also use search in combination with filters to drill down further into the list of shipments. For more information, see Searching Shipments.
Editing Pre-enrolled Shipments
Just as for other types of shipments, you can update a pre-enrolled shipment from the Customer Portal until it is locked for processing and fulfillment. Shipments that can be edited are indicated with an Edit icon in the Shipment status column of the Shipments page.
You can update the recipient and address information, the delivery type, or you can delete the shipment request. Note that products included in a pre-enrolled shipment request cannot be modified. For more information, see Editing and Deleting Shipments.
Viewing Customization Information
A pre-enrolled YubiKey is considered a customization, and therefore Yubico provides a unique Customization ID which is also required for the FIDO Pre-reg integration. To view your organization’s Customization ID, see Customizations.